A New Seamanship Practice: Cyber-Discipline
‘Discipline in any form is a management tool to enforce organizational standards…Any action taken to reduce infractions and encourage employees to maintain standards and follow an expected format is known as preventive discipline. The objective being to develop employees to operate under a code of self-discipline as opposed to a management-imposed discipline level.’
– D J House, The Command Companion of Seamanship Techniques
In February 2017, hackers took control of the navigation systems of a large container ship for about 10 hours. Fortunately, the situation was brought under control and as a result, there was no casualty.
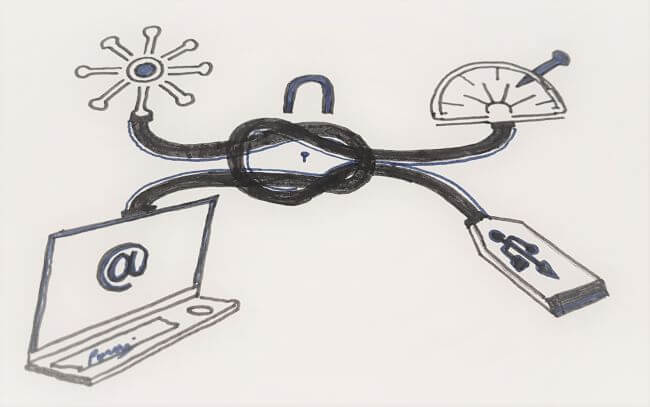
It’s not always so dramatic; over 50% of cybersecurity threats arise from improper use of IT systems by users, rather than external hacks. Cyber-Awareness-Discipline then becomes the primary control against these threats, and it becomes every mariner’s responsibility to help secure the ship’s IT network. In today’s connected world, cyber-discipline has become as important as in seamanship practice as the knowledge of knots and splices.
Physical Security
• Ships operational technology (e.g. valve-control system, cargo-loading program, ECDIS, engine control system) should not be connected to the internet unless it is through a secure gateway. USBs or mobile devices should not be connected to these systems except when unavoidable e.g. for ECDIS updates where only IT-department approved USBs should be used. No other files should be uploaded on these flash drives.
The sailing of a large tanker was delayed due to an infected USB. One of the crew had brought a USB stick on board with some paperwork that needed to be printed. The malware got into the ship’s computers. Things got worse when another crew member used the same USB to update the ship’s charts before sailing. The navigation systems became infected and the departure of the ship was consequently delayed.2
• Format any new USB before using them. Don’t allow your computer to automatically open any USB devices. Attach a lanyard to a centralized location to avoid misplacing the dedicated USBs for the ECDIS.
• Servers and gateways should be placed in locked cabinets or spaces.
• Business networks should be separate from crew networks. Personal material should not be uploaded to work terminals, and vice-versa.
• IT and control terminals should be accessible only with passwords, with auto-logoff after about 3 minutes of inactivity.
• Do not provide unsupervised access to unauthorized personnel. When third-party technicians require access, ensure there is adequate supervision.
• Computers must be restricted in downloading or adding any software and allowed by administrator only.
A container ship’s switchboard was shut down after ransomware found its way on the vessel. The ship’s operations were interrupted due to the power management systems being affected.2
• All terminals must be returned to the IT department for proper decommissioning.
Passwords
• Default passwords should be changed after the initial access and changed periodically. Passwords should be at least 8 characters, including one Uppercase, one number and one symbol.
• Do not write or keep passwords written near input points. Do not share passwords with other personnel.
• Administrator privileges should only be given to appropriately trained and designated personnel.
- Do not leave passwords close to the terminals
Email and Internet use
• Do not open attachments from unknown sources. Especially beware of attachments which end with .pdf or .exe.
In the Saudi Aramco case- about 30,000 computers of the world’s largest oil company were infected with a virus which started by an employee clicking on a bad email link.
• Any email from an unknown source which urges the reader to act fast (e.g. ‘only available today – get free pills’) can contain malicious links.
• Don’t be misled by official looking emails, logos and names. Watch the correct email address and incongruent links. Remember that emails purporting to be from large organizations do not use email addresses with Gmail or Yahoo domains.Spelling or grammar errors can indicate the email may be fraudulent.
• Avoid opening emails which request a payment or with a link to a payment portal.
• Be careful of links for surveys.Never fill out forms in the email. Beware of emails asking for personal information or asking to verify personal details/ bank details.
• Use safe websites: A URL that uses https at the start of it (instead of http) uses encryption and is safe to use. Beware of deceptive URLs e.g. https://www.abcbanklogin.com instead of https://www.login.abcbank.com which is the secure website.
• Do not use open Wi-Fi (such as in coffee shops) for financial transactions, sensitive or confidential emails, or online meetings.
• Do not use illegal or unlicensed software. It is insecure and illegal.
Maintenance
• Backup your data as per the planned schedule. Regularly back up files stored on your computer, tablet, and smartphone. Ship’s planned-maintenance data should also be backed up in the office. If your machine becomes infected with malware, these backups can be used to restore your system. If performing your own backups, unplug your external hard drive after every manual backup.
• Other checks include – Update of anti-virus, firewalls and patches. Change passwords every quarter. Check that USB ports are blocked. Check that software and applications are updated to the latest version. Penetration tests are carried out annually by the IT department.
Training:
• Cybersecurity awareness should be part of the familiarization checklist. Train your team on the detection and reporting of cybersecurity breaches.
• Navigators should routinely cross-check their GPS-ECDIS positions with other means of position fixing so they are aware of the backup means of navigation in case the use of GPS-ECDIS is compromised.
• Cyber-security breach drills should be practised as part of the Safety Management System drill schedule.
About the author:
Captain VS Parani, FNI, FICS, CMarTech-IMarESTis the author of Golden Stripes- Leadership on the High Seas, and writes blogs on maritime-leadership at parani.org.
Do you have info to share with us ? Suggest a correction
Latest Shipboard Guidelines Articles You Would Like:
Subscribe To Our Newsletters
By subscribing, you agree to our Privacy Policy and may receive occasional deal communications; you can unsubscribe anytime.















The luxuries (ECDIS & other IT systems) of today are becoming the necessities of tomorrow. Is this the beginning of the end of such traditional seafaring skills as navigation and cargo handling.?
@Vetus: I don’t think so. The technology is growing fast and rather considering it as the “end” of traditional skills, I choose to use the “improvise”.